Poging GOUD - Vrij
The Linux System Call Execution Model: An Insight
Open Source For You
|August 2024
This two-part series of articles focuses on the system call execution model in Linux based operating systems. This first part explains what system calls are, why they are required and the role of the glibc wrapper in system call execution. It then touches on the system call execution model from the Linux kernel perspective.
-
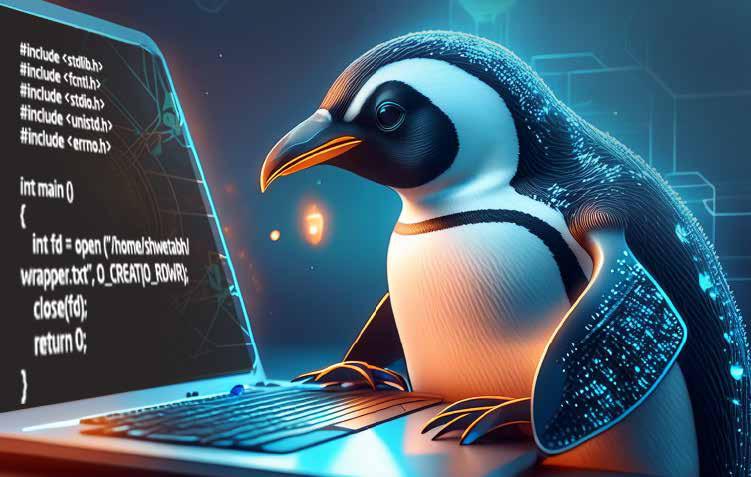
A system call is a request by a user space program (application) to interact with an OS executing in the kernel space. Basically, the user application invokes a system call when it requires access to the services that can only be accessed through a higher privilege mode — for example, creating a new task, doing network I/O or file I/O, or accessing hardware resources. These operations cannot be directly performed by the user space application; hence, operating systems like Linux provide a set of routines called system calls which are basically C functions executing in the kernel space.
When a user space program invokes a system call, there is a software interrupt (nowadays x86-64 provides syscall instruction for fast system call execution) and the mode switches from user space to kernel space (or more precisely, the privilege mode changes from lower to higher). Now the system call handler in the kernel space performs the required operation on behalf of the user space application and sends the response back to it.
We will see in detail in later sections as to how the user space to kernel space mode switching happens and how kernel space system call handlers are invoked. But first let’s examine the role of the standard C library in the execution of system calls.
 Role of the C library
Role of the C library When we say C library, the most commonly and widely distributed C library with a Linux based OS is glibc or GNU C library. This C library helps implement standard C functions and APIs like print(), scanf(), malloc(), fopen(), strcpy(), etc. These standard functions may or may not invoke system calls internally — for example, printf() internally invokes write(2)
Dit verhaal komt uit de August 2024-editie van Open Source For You.
Abonneer u op Magzter GOLD voor toegang tot duizenden zorgvuldig samengestelde premiumverhalen en meer dan 9000 tijdschriften en kranten.
Bent u al abonnee? Aanmelden
MEER VERHALEN VAN Open Source For You

Open Source For You
Sending IoT Sensor Data to Public or Private Servers
This IoT system shows a simple and effective way to send sensor data using an ESP8266 microchip.
3 mins
March 2026

Open Source For You
Popular FOSS Tools for LLM Observability, Monitoring and Evaluation
This overview of popular tools for monitoring large language models also sheds light on how LLM-as-a-judge enhances their performance.
2 mins
March 2026

Open Source For You
Data Deduplication Done the Right Way
Deduplication helps to save space on Linux-based storage systems. Choose the right platform and check whether it meets your goals.
6 mins
March 2026

Open Source For You
The Relevance of Rubber Duck Debugging in the Age of AI
Discover why rubber duck debugging is a powerful process today. There's also a step-by-step guide on how to use it in the age of artificial intelligence.
4 mins
March 2026

Open Source For You
GitHub weighs turning off pull requests as AĬ slop floods projects
GitHub has formally acknowledged that AI-generated 'slop' is overwhelming open source projects, forcing maintainers to sift through poor pull requests (PRS), abandoned submissions and guideline violations - and is now considering restricting or even disabling pull requests, the core mechanism of open collaboration.
1 min
March 2026

Open Source For You
Global banks are deploying Ethereum's Layer-2 stack
Banks are standardising on Ethereum's open source stack as production financial infrastructure, shifting from experimental pilots and proprietary blockchains to live Layer-2 networks for tokenised deposits, interbank payments, and cross-border settlement.
1 min
March 2026

Open Source For You
OpenClaw's creator joins OpenAl
In a move that reinforces its commitment to open development rather than acquisition, OpenAI has brought Peter Steinberger, founder of OpenClaw, into the company while placing the popular AI agent under a foundation structure to ensure it remains open source.
1 min
March 2026
Open Source For You
LibreOffice 26.2 comes with native Markdown support
LibreOffice 26.2 has been released by The Document Foundation, strengthening its position as a fully free and open source office suite for Windows, macOS, and Linux, with support for more than 120 languages.
1 min
March 2026

Open Source For You
Indian government mandates labelling of Al-generated content and quicker deletion of illegal deepfakes
India has introduced sweeping AI content rules that immediately place pressure on social platforms and open source AI ecosystems to label, trace and rapidly remove AI Open ource synthetic media at scale.
1 min
March 2026

Open Source For You
I2C and I3C: How Modern Devices Communicate
I3C and I2C are both two-wire communication protocols that help exchange data between multiple devices. While I3C preserves the simplicity of I2C, it introduces new features suited for today's sensor-rich devices.
8 mins
March 2026
Listen
Translate
Change font size

