Poging GOUD - Vrij
OpenVAS: The Popular Vulnerability Assessment Tool
Open Source For You
|December 2025
Here's a comprehensive guide to how you can use OpenVAS to fix potential security issues before they crop up.
In an era where organisations gravitate towards new technologies, finding and fixing security weaknesses is mandatory.
The process of identifying potential problems before these can be exploited by attackers is known as vulnerability analysis.
One of the most common open source tools used for this is OpenVAS (Open Vulnerability Assessment System), which is part of the Greenbone Vulnerability Management (GVM) framework. Let's see how we can use this tool effectively.
Installing and accessing OpenVAS
First, we must have Docker on our system. If it's not already installed, let's open a terminal and run the necessary commands to set it up.
$ sudo apt install docker.io
We can now use a single command to download the OpenVAS image and start it as a container.
$ sudo docker run -d -p 443:443 --name openvas mikesplain/openvas
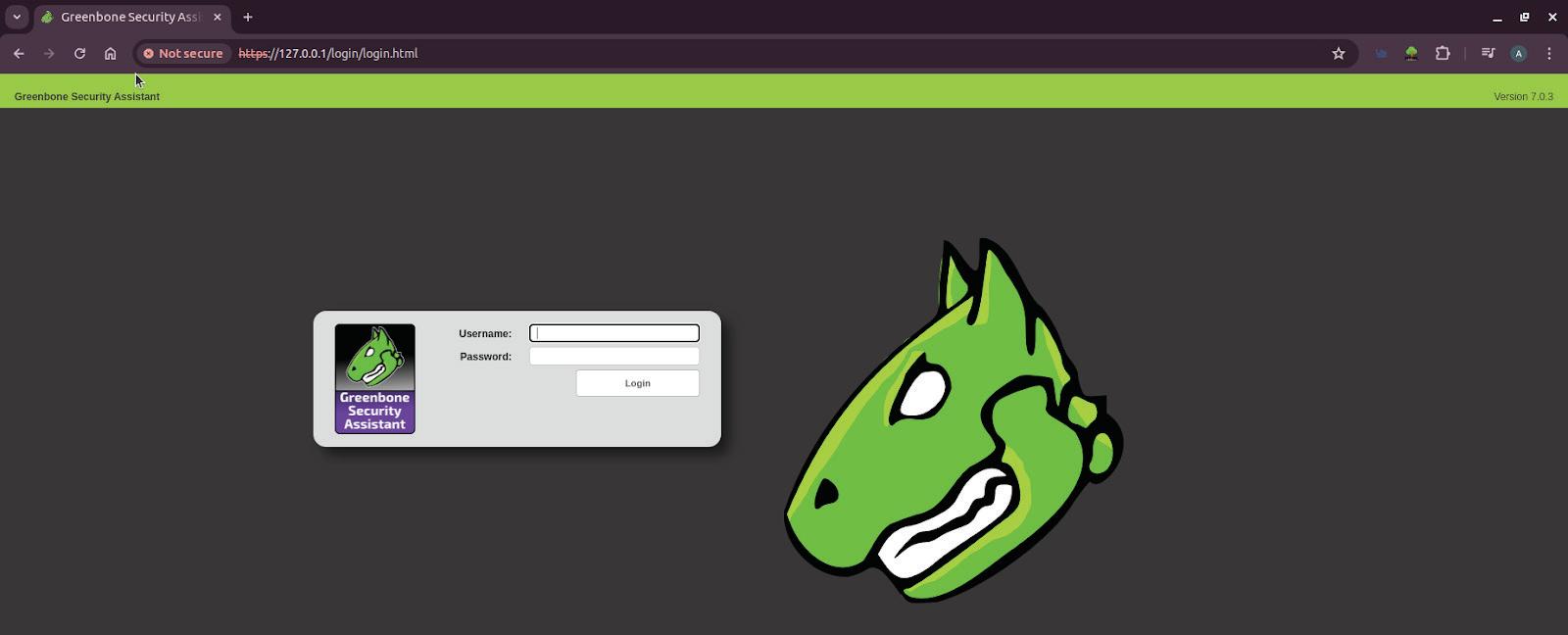
Open a browser window and type https://127.0.0.1 for the login page (as shown in Figure 1). Enter the username as admin and password also as admin. The interface looks like what's shown in Figure 1. We can change the username and password later.
After logging in, the interface looks like what is shown in Figure 2.
Performing a vulnerability scan
To perform a vulnerability scan on a target system to identify potential security vulnerabilities, click on the magic wand icon on the top left. We get the task wizard working as shown in Figure 3. Then we can enter the IP address in the text box. In this demo, I tested for vulnerabilities with two IP addresses -- 172.17.0.1 and a vulnerable public IP address 45.33.32.156. Now click on the Start scan button.
Analysing scan results
Dit verhaal komt uit de December 2025-editie van Open Source For You.
Abonneer u op Magzter GOLD voor toegang tot duizenden zorgvuldig samengestelde premiumverhalen en meer dan 9000 tijdschriften en kranten.
Bent u al abonnee? Aanmelden
MEER VERHALEN VAN Open Source For You

Open Source For You
Top 10 Open Source Tools for System and IT Administrators
All reputed online services have committed system and IT administrators working behind the scenes. Here are ten open source tools they should be aware of, as these can help them monitor, automate, as well as manage complex infrastructure with relative ease.
6 mins
February 2026
Open Source For You
Google opens access to its Gemini Deep Research Agent
Google has opened access to its Gemini Deep Research Agent for the first time, allowing developers to integrate advanced autonomous research capabilities directly into their applications.
1 min
February 2026

Open Source For You
NVIDIA buys SchedMD, keeps Slurm open source and vendor neutral
NVIDIA has acquired AI software company SchedMD, signalling a deeper commitment to open source technologies as competition intensifies across the artificial intelligence ecosystem.
1 min
February 2026

Open Source For You
How Open Source Tools Power Modern IT Operations
Open source tools have not replaced enterprise IT platforms; they have become the connective layer that makes modern operations possible.
6 mins
February 2026
Open Source For You
Mandiant's Auralnspector enhances Salesforce security
Google-owned cybersecurity firm Mandiant has released AuraInspector, a free, open source command-line tool designed to identify dangerous access control misconfigurations in Salesforce environments, marking a significant move to democratise enterprise-grade security testing.
1 min
February 2026
Open Source For You
Google launches Universal Commerce Protocol to power agentic AI commerce
Google has introduced the Universal Commerce Protocol (UCP), a new open standard that enables AI agents to autonomously perform end-to-end commerce activities, spanning product discovery, purchasing, checkout, payments, and postpurchase experiences.
1 min
February 2026

Open Source For You
Zero Trust CI/CD: The Death of Static Secrets
In an era where data breach costs continue to hit record highs, shifting to a secretless CI/CD pipeline is the most effective step to safeguard digital infrastructure.
7 mins
February 2026

Open Source For You
Quantum Algorithms: The Future of Computing
Explore the essence of quantum algorithms, their groundbreaking applications, recent innovations, and the challenges that remain.
8 mins
February 2026

Open Source For You
Bringing Clarity to the Chaos in AI
AI feels powerful, yet most teams struggle because they cannot define what intelligence they really need. But there are ways to address this challenge.
5 mins
February 2026

Open Source For You
Top researchers return to OpenAI
OpenAI has welcomed back three high-profile researchers, Barret Zoph, Luke Metz, and Sam Schoenholz, following their brief tenure at former OpenAI CTO Mira Murati's AI startup, Thinking Machines.
1 min
February 2026
Listen
Translate
Change font size

